As we near our 10,000th pentest, today we are proud to publish the fifth edition of our annual research report The State of Pentesting.
The 2023 report taps into data from over 3,100 pentests we did in 2022, and 1,000 responses from security teams in the US, the UK, and Germany. The results reveal the most prevalent vulnerabilities from 2022 and answer questions like…
- What did our pentester community find most often in web apps, APIs, networks, and cloud configurations?
- Which were the highest severity vulnerabilities? And which low-risk issues could chain into larger exploits?
- How have economic disruptions like reductions in workforce and budgets affected enterprises’ security?
- What can security teams do to achieve more results with fewer resources?
Let’s dive into the results.
Which are the most common security issues?
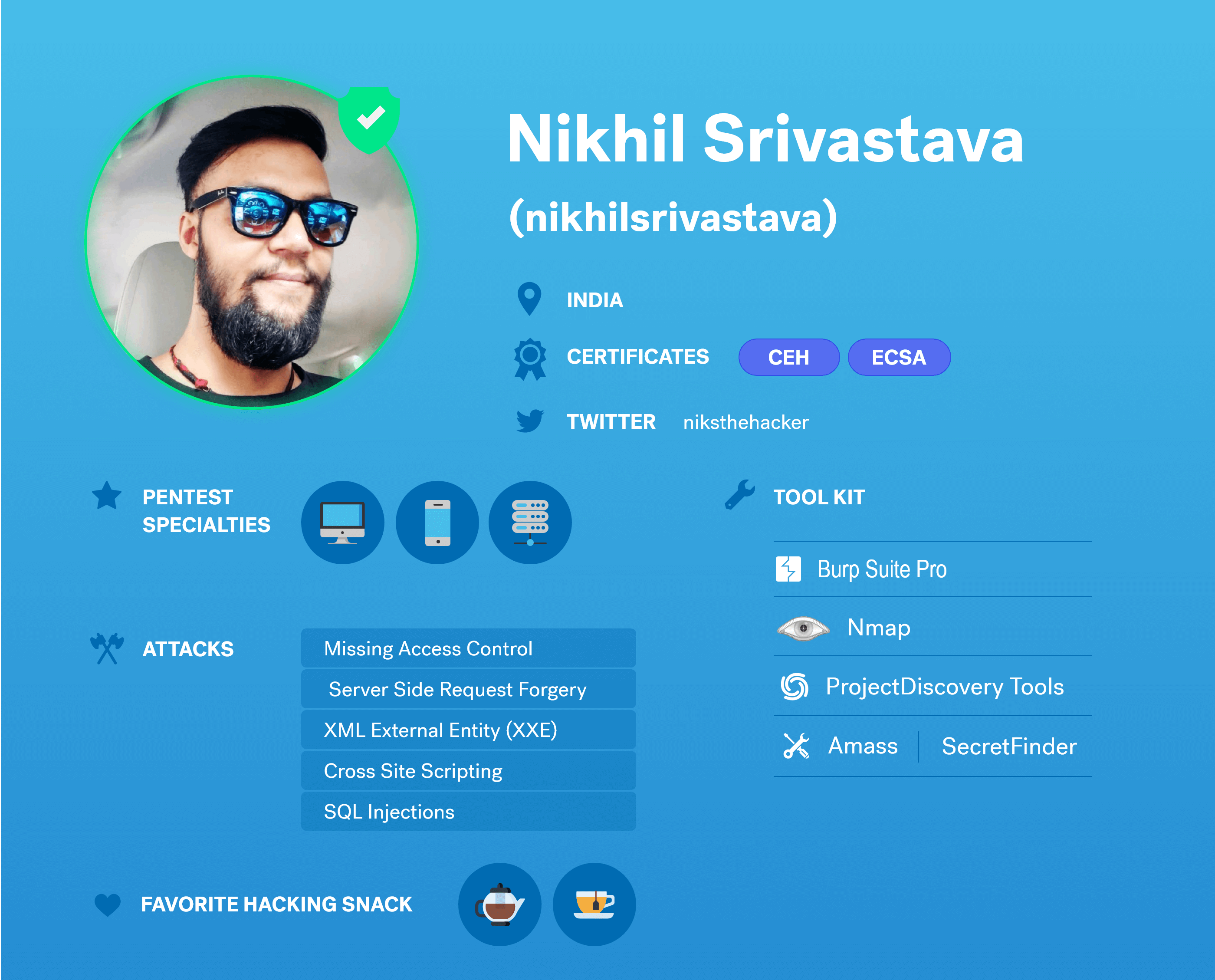
In 2022, we discovered more than 16,000 findings. The 5 most prevalent issues across all assets include:
- Stored Cross-Site Scripting
- Outdated Software Versions
- Insecure Direct Object References (IDOR)
- Lack of Security Headers
- Insecure Secure Sockets Layer (SSL) and Transport Layer Security (TLS) Protocols
It’s worth noting that two of the three most repetitive flaws — Stored Cross-Site Scripting and Insecure Direct Object References — have the potential for serious damage. Our pentesters marked them frequently as Medium or High severity, meaning they could have a high business impact if exploited.
How to prevent Cross-Site Scripting?
Any feature that allows user input can be vulnerable, because it gives attackers an opportunity to inject and store malicious content into web applications. To prevent this, Cobalt recommends treating all user-supplied input as untrusted data and accepting input in select locations. We also recommend using a well-known and secure encoding API for input and output encoding, such as the OWASP ESAPI.
How to prevent Insecure Direct Object References (IDOR)?
This vulnerability can give access to resources via user-supplied input, where attackers bypass authorization by modifying a value of a parameter that points directly to an object in your database. Use per-user or per-session indirect object references. Each time your application uses a direct object reference from an untrusted source, it should also make an access control check to ensure that the user is authorized to access the requested object.
Teams are struggling to maintain security standards due to operational changes
High employee turnover and scant bandwidth still hamstring productivity, with mounting pressure to restructure and cut costs amidst speculation of a downturn.
In the US, 77% of respondents shared that their department had been directly impacted by company layoffs in the last six months. 63% also shared their budgets had been cut — on average, by 31%.
In the UK and Germany, fewer teams reported the same struggles — 25% said their security team had been affected by layoffs, and 28% said their budgets had been cut. Does that mean they’re in a much better position to maintain a strong security posture? Not necessarily. Cybersecurity works as a global ecosystem, where one exploit may trigger a domino effect across the supply chain. Looking at the US stats, it’s safe to say the whole system is put under strain.
And what might that strain be, exactly? Teams affected by organizational changes report unmanageable workloads, challenges in maintaining security standards, as well as monitoring for vulnerabilities.
76% of teams in the US and 65% in the UK and Germany even went so far as to report that fewer resources had led to backlogs of unaddressed vulnerabilities in 2022, and over 80% of respondents, regardless of geographies, said this problem would worsen in the coming months. It should come as no surprise that teams across the board are planning to either deprioritize or outsource a variety of tasks — 74% in the US plan to outsource more in 2022, while 66% in the UK and Germany are de-prioritizing projects to stay focused on bigger priorities.
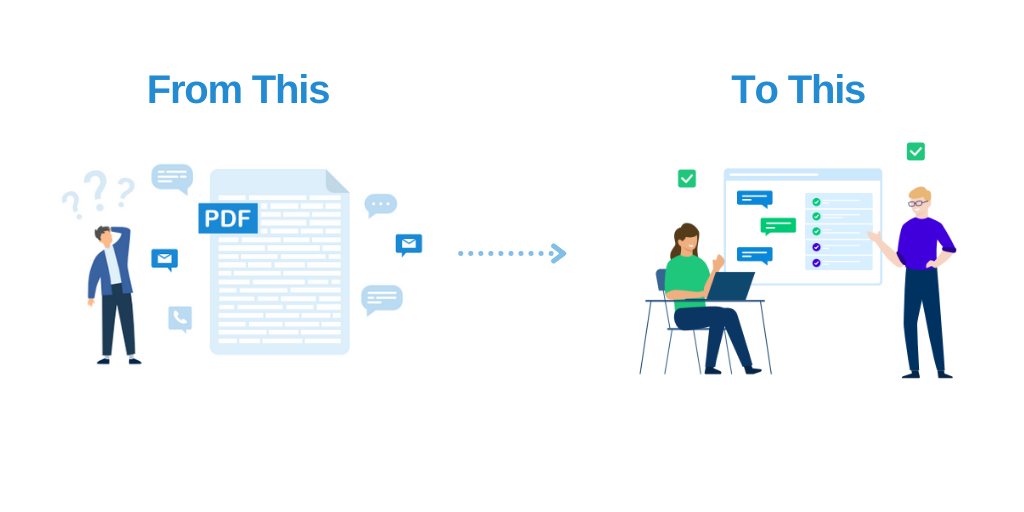
Teams have to make every minute and penny count
These stats confirm that, more than ever before, teams are pushed to achieve more results with much fewer resources. And yet, many reported that they struggle to make the most out of their pentests.
A challenge respondents from all geographies shared was preparing their environment for the pentest. This can be a pivotal component that hinders efficiency and hurts the final result, not to mention cause business disruptions if tests take place in production.
What can teams do to make every pentest count and extract maximum ROI? The 3rd part of our report shares detailed instructions on how to prepare not just your environment, but also your documentation and colleagues. Download the Pentest Preparation Checklist, or get all the details by downloading The State of Pentesting 2023 Report.